How PDF Fraud Works and What to Look For
Digital documents are deceptively easy to manipulate. Understanding the common tactics used to create a fake or altered PDF is the first step in defending against fraud. Attackers commonly edit text, swap pages, embed images of signatures, or change metadata to hide the trail of modifications. They may also produce visually convincing invoices and receipts that mimic authentic suppliers by copying logos, fonts, and layout. Recognizing these patterns requires attention to both content and file-level indicators.
Examine the document beyond its appearance. Metadata such as creation date, modification date, and author fields can reveal inconsistencies—an invoice dated last month but created yesterday or a receipt whose creator field doesn’t match the vendor should raise suspicion. Look for mismatched fonts, uneven alignment, and image artifacts that indicate pasted elements. Watermarks, microtext, or embedded fonts that don’t match the rest of the document are red flags. Even legitimate-looking documents may contain structural anomalies like multiple embedded files or unusual object streams.
Financial documents often contain numeric cues that betray tampering. Totals that do not reconcile with line-item math, altered tax rates, or inconsistent currency formats are telltale signs. Compare suspicious documents against a trusted template or past invoices from the same vendor—subtle layout shifts, different invoice numbering schemes, or changed bank details indicate potential fraud. Train teams to verify unusual payment instructions directly with the vendor using previously established contact channels rather than relying on contact details present in the suspicious PDF.
Tools, Techniques, and Workflows to Detect Fraud in PDF Files
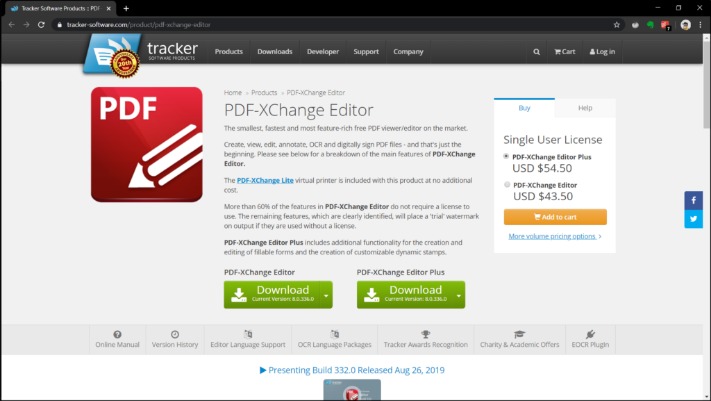
Automated and manual techniques together yield the best results at scale. Begin with a layered workflow: perform quick visual checks, run file-level analysis, and escalate to forensic inspection if needed. Use PDF viewers that expose metadata and object trees to inspect embedded elements and attachments. Optical Character Recognition (OCR) helps compare scanned images to extracted text to detect pasted or retyped sections. Hashing and version comparison tools will identify changes between document versions.
Specialized services and software can accelerate detection. Content analysis algorithms look for pattern anomalies, font substitutions, and alignment inconsistencies, while signature verification tools examine digital signatures and certificates for validity. For organizations that receive many invoices and receipts, integrating a verification step in the accounts payable workflow reduces risk. Automated flags for mismatched vendor names, abnormal amounts, or changed payment accounts cut down on human error. For a quick check on questionable documents, use dedicated online tools to detect fake invoice with automated tests for metadata, signatures, and common forgery markers.
Best practice is to combine technical controls with process safeguards: maintain whitelists of vendor templates, require two-person approval for large payments, and use multi-factor authentication for financial approvals. Regular training for staff to spot social-engineering attempts and suspicious document cues increases detection rates. When tampering is suspected, preserve the original file and its transmission context (email headers, attachments, download logs) to support any necessary investigation.
Real-World Examples, Case Studies, and Practical Recommendations
Several high-profile cases illustrate how simple manipulations can lead to substantial loss. In one scenario, an accounts payable team paid an altered invoice after the fraudster changed the bank details on a legitimate PDF and sent it from a lookalike email address. The escape hatch was a change in the digits of the routing number—easy to overlook during a busy pay cycle. Another case involved a scanned receipt where the total had been incremented using a pasted image of numbers; OCR comparison against the raw text revealed the mismatch and prevented reimbursement fraud.
Organizations that successfully reduced losses combined automation with clear verification rules. A mid-sized firm implemented template-matching software that compared incoming invoices to known vendor formats and flagged deviations for manual review. That single control lowered fraudulent payments by over 60% within six months. Another nonprofit required verbal confirmation of any vendor account change before processing payments; the added friction stopped multiple attempted bank-detail hijacks.
Practical recommendations: enforce strict vendor onboarding and change procedures, retain copies of verified vendor templates, and require multiple approvers for high-risk transactions. Use both simple checks—confirm math, inspect metadata, and validate contact details—and advanced tools like digital-signature validation and forensic PDF analysis when suspicion arises. Combining these measures turns the advantage back to defenders and makes it far harder for fraud to succeed.